< < TM03.4 : TM04.1 : TM04.2 > >
TM04.1: Pre-Timed (Fixed Time) Control Implementation
The basic signal control implementation offered in TM03 is extended with Connected Vehicle Roadside Equipment installed at the intersection that supports real-time communications between the intersection and approaching vehicles. Detailed status is collected from approaching vehicles and real-time intersection status is provided so that approaching and queued vehicles can optimize their intersection use. In this basic implementation, signal timing is fixed and independent of data collected from approaching vehicles and/or traditional infrastructure-based detectors.
Relevant Regions: Australia, Canada, European Union, and United States
- Enterprise
- Functional
- Physical
- Goals and Objectives
- Needs and Requirements
- Sources
- Security
- Standards
- System Requirements
Enterprise
Development Stage Roles and Relationships
Installation Stage Roles and Relationships
Operations and Maintenance Stage Roles and Relationships
(hide)
| Source | Destination | Role/Relationship |
|---|---|---|
| Connected Vehicle Roadside Equipment Maintainer | Connected Vehicle Roadside Equipment | Maintains |
| Connected Vehicle Roadside Equipment Manager | Connected Vehicle Roadside Equipment | Manages |
| Connected Vehicle Roadside Equipment Manager | Connected Vehicle Roadside Equipment Operator | System Usage Agreement |
| Connected Vehicle Roadside Equipment Operator | Connected Vehicle Roadside Equipment | Operates |
| Connected Vehicle Roadside Equipment Owner | Connected Vehicle Roadside Equipment Maintainer | System Maintenance Agreement |
| Connected Vehicle Roadside Equipment Owner | Connected Vehicle Roadside Equipment Manager | Operations Agreement |
| Connected Vehicle Roadside Equipment Owner | Driver | Application Usage Agreement |
| Connected Vehicle Roadside Equipment Owner | ITS Roadway Equipment Maintainer | Maintenance Data Exchange Agreement |
| Connected Vehicle Roadside Equipment Owner | ITS Roadway Equipment Owner | Information Exchange and Action Agreement |
| Connected Vehicle Roadside Equipment Owner | ITS Roadway Equipment User | Service Usage Agreement |
| Connected Vehicle Roadside Equipment Owner | Maint and Constr Field Personnel | Application Usage Agreement |
| Connected Vehicle Roadside Equipment Owner | Traffic Management Center Maintainer | Maintenance Data Exchange Agreement |
| Connected Vehicle Roadside Equipment Owner | Traffic Management Center Owner | Information Exchange Agreement |
| Connected Vehicle Roadside Equipment Owner | Traffic Management Center User | Service Usage Agreement |
| Connected Vehicle Roadside Equipment Owner | Traffic Operations Personnel | Application Usage Agreement |
| Connected Vehicle Roadside Equipment Owner | Vehicle Maintainer | Maintenance Data Exchange Agreement |
| Connected Vehicle Roadside Equipment Owner | Vehicle Owner | Expectation of Information Provision |
| Connected Vehicle Roadside Equipment Owner | Vehicle User | Service Usage Agreement |
| Connected Vehicle Roadside Equipment Supplier | Connected Vehicle Roadside Equipment Owner | Warranty |
| Driver | Vehicle | Operates |
| ITS Roadway Equipment Maintainer | ITS Roadway Equipment | Maintains |
| ITS Roadway Equipment Manager | ITS Roadway Equipment | Manages |
| ITS Roadway Equipment Manager | Maint and Constr Field Personnel | System Usage Agreement |
| ITS Roadway Equipment Owner | Connected Vehicle Roadside Equipment Maintainer | Maintenance Data Exchange Agreement |
| ITS Roadway Equipment Owner | Connected Vehicle Roadside Equipment Operator | Application Usage Agreement |
| ITS Roadway Equipment Owner | Connected Vehicle Roadside Equipment Owner | Information Exchange and Action Agreement |
| ITS Roadway Equipment Owner | Connected Vehicle Roadside Equipment User | Service Usage Agreement |
| ITS Roadway Equipment Owner | ITS Roadway Equipment Maintainer | System Maintenance Agreement |
| ITS Roadway Equipment Owner | ITS Roadway Equipment Manager | Operations Agreement |
| ITS Roadway Equipment Owner | Other ITS Roadway Equipment Maintainer | Maintenance Data Exchange Agreement |
| ITS Roadway Equipment Owner | Other ITS Roadway Equipment Operator | Application Usage Agreement |
| ITS Roadway Equipment Owner | Other ITS Roadway Equipment Owner | Information Exchange and Action Agreement |
| ITS Roadway Equipment Owner | Other ITS Roadway Equipment User | Service Usage Agreement |
| ITS Roadway Equipment Owner | Traffic Management Center Maintainer | Maintenance Data Exchange Agreement |
| ITS Roadway Equipment Owner | Traffic Management Center Owner | Information Exchange Agreement |
| ITS Roadway Equipment Owner | Traffic Management Center User | Service Usage Agreement |
| ITS Roadway Equipment Owner | Traffic Operations Personnel | Application Usage Agreement |
| ITS Roadway Equipment Supplier | ITS Roadway Equipment Owner | Warranty |
| Maint and Constr Field Personnel | ITS Roadway Equipment | Operates |
| Other ITS Roadway Equipment Maintainer | Other ITS Roadway Equipment | Maintains |
| Other ITS Roadway Equipment Manager | Other ITS Roadway Equipment | Manages |
| Other ITS Roadway Equipment Manager | Other ITS Roadway Equipment Operator | System Usage Agreement |
| Other ITS Roadway Equipment Operator | Other ITS Roadway Equipment | Operates |
| Other ITS Roadway Equipment Owner | ITS Roadway Equipment Maintainer | Maintenance Data Exchange Agreement |
| Other ITS Roadway Equipment Owner | ITS Roadway Equipment Owner | Information Exchange and Action Agreement |
| Other ITS Roadway Equipment Owner | ITS Roadway Equipment User | Service Usage Agreement |
| Other ITS Roadway Equipment Owner | Maint and Constr Field Personnel | Application Usage Agreement |
| Other ITS Roadway Equipment Owner | Other ITS Roadway Equipment Maintainer | System Maintenance Agreement |
| Other ITS Roadway Equipment Owner | Other ITS Roadway Equipment Manager | Operations Agreement |
| Other ITS Roadway Equipment Supplier | Other ITS Roadway Equipment Owner | Warranty |
| TIC Operator | Transportation Information Center | Operates |
| Traffic Management Center Maintainer | Traffic Management Center | Maintains |
| Traffic Management Center Manager | Traffic Management Center | Manages |
| Traffic Management Center Manager | Traffic Operations Personnel | System Usage Agreement |
| Traffic Management Center Owner | Connected Vehicle Roadside Equipment Maintainer | Maintenance Data Exchange Agreement |
| Traffic Management Center Owner | Connected Vehicle Roadside Equipment Operator | Application Usage Agreement |
| Traffic Management Center Owner | Connected Vehicle Roadside Equipment Owner | Information Exchange Agreement |
| Traffic Management Center Owner | Connected Vehicle Roadside Equipment User | Service Usage Agreement |
| Traffic Management Center Owner | ITS Roadway Equipment Maintainer | Maintenance Data Exchange Agreement |
| Traffic Management Center Owner | ITS Roadway Equipment Owner | Information Exchange Agreement |
| Traffic Management Center Owner | ITS Roadway Equipment User | Service Usage Agreement |
| Traffic Management Center Owner | Maint and Constr Field Personnel | Application Usage Agreement |
| Traffic Management Center Owner | TIC Operator | Application Usage Agreement |
| Traffic Management Center Owner | Traffic Management Center Maintainer | System Maintenance Agreement |
| Traffic Management Center Owner | Traffic Management Center Manager | Operations Agreement |
| Traffic Management Center Owner | Transportation Information Center Maintainer | Maintenance Data Exchange Agreement |
| Traffic Management Center Owner | Transportation Information Center Owner | Information Provision Agreement |
| Traffic Management Center Owner | Transportation Information Center User | Service Usage Agreement |
| Traffic Management Center Supplier | Traffic Management Center Owner | Warranty |
| Traffic Operations Personnel | Traffic Management Center | Operates |
| Transportation Information Center Maintainer | Transportation Information Center | Maintains |
| Transportation Information Center Manager | TIC Operator | System Usage Agreement |
| Transportation Information Center Manager | Transportation Information Center | Manages |
| Transportation Information Center Owner | Driver | Application Usage Agreement |
| Transportation Information Center Owner | Transportation Information Center Maintainer | System Maintenance Agreement |
| Transportation Information Center Owner | Transportation Information Center Manager | Operations Agreement |
| Transportation Information Center Owner | Vehicle Maintainer | Maintenance Data Exchange Agreement |
| Transportation Information Center Owner | Vehicle Owner | Information Provision Agreement |
| Transportation Information Center Owner | Vehicle User | Service Usage Agreement |
| Transportation Information Center Supplier | Transportation Information Center Owner | Warranty |
| Vehicle Maintainer | Vehicle | Maintains |
| Vehicle Manager | Driver | System Usage Agreement |
| Vehicle Manager | Vehicle | Manages |
| Vehicle Owner | Connected Vehicle Roadside Equipment Maintainer | Maintenance Data Exchange Agreement |
| Vehicle Owner | Connected Vehicle Roadside Equipment Operator | Application Usage Agreement |
| Vehicle Owner | Connected Vehicle Roadside Equipment Owner | Expectation of Data Provision |
| Vehicle Owner | Connected Vehicle Roadside Equipment User | Service Usage Agreement |
| Vehicle Owner | Vehicle Maintainer | System Maintenance Agreement |
| Vehicle Owner | Vehicle Manager | Operations Agreement |
| Vehicle Supplier | Vehicle Owner | Warranty |
Functional
This service package includes the following Functional View PSpecs:
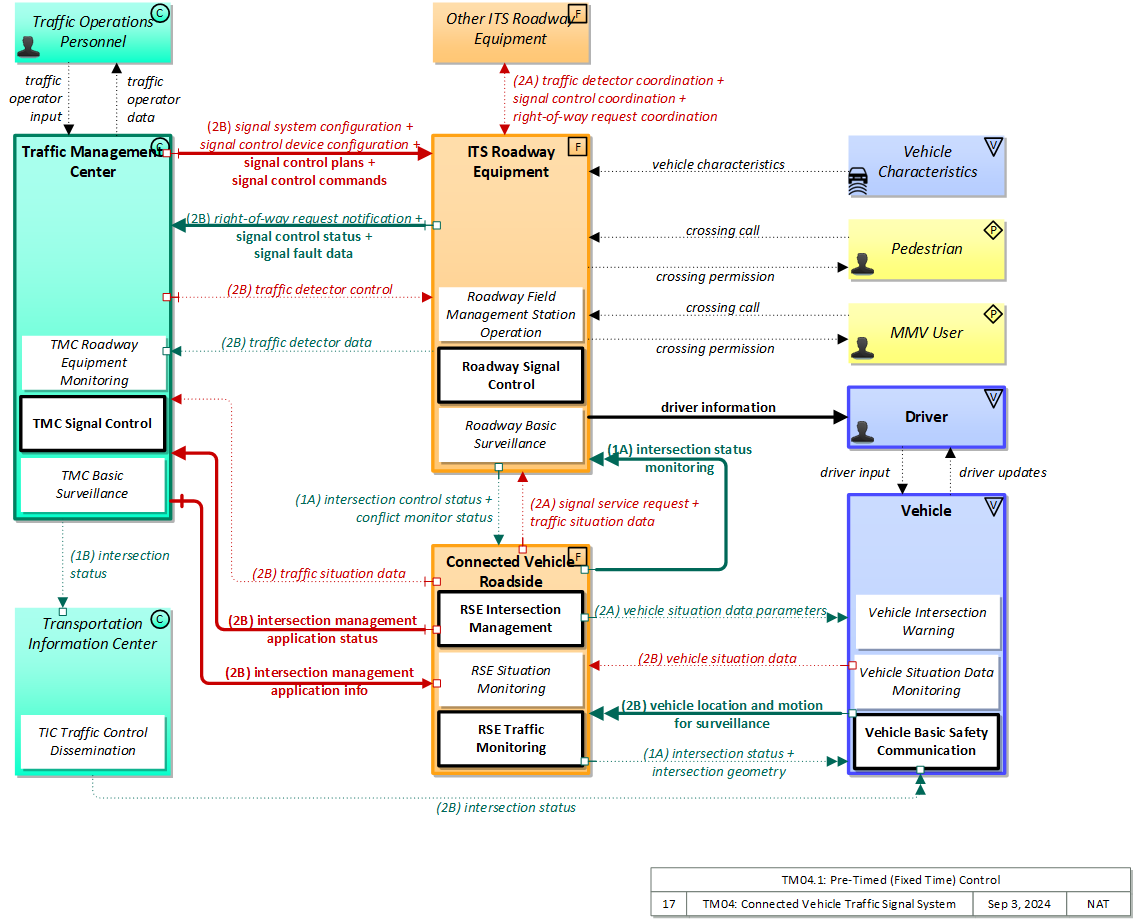
Physical
The physical diagram can be viewed in SVG or PNG format and the current format is SVG.SVG Diagram
PNG Diagram
Includes Physical Objects:
| Physical Object | Class | Description |
|---|---|---|
| Connected Vehicle Roadside Equipment | Field | 'Connected Vehicle Roadside Equipment' (CV RSE) represents the Connected Vehicle roadside devices (i.e., Roadside Units (RSUs)) equipped with short range wireless (SRW) communications technology, as well as any other supporting equipment that leverage the RSU and are not described by other objects (e.g., a local roadside processor). CVRSE are used to send messages to, and receive messages from, nearby vehicles and personal devices equipped with compatible communications technology. Communications with adjacent field equipment and back office centers that monitor and control the RSE are also supported. This device operates from a fixed position and may be permanently deployed or a portable device that is located temporarily in the vicinity of a traffic incident, road construction, or a special event. It includes a processor, data storage, and communications capabilities that support secure communications with passing vehicles, other field equipment, and centers. |
| Driver | Vehicle | The 'Driver' represents the person that operates a vehicle on the roadway. Included are operators of private, transit, commercial, and emergency vehicles where the interactions are not particular to the type of vehicle (e.g., interactions supporting vehicle safety applications). The Driver originates driver requests and receives driver information that reflects the interactions which might be useful to all drivers, regardless of vehicle classification. Information and interactions which are unique to drivers of a specific vehicle type (e.g., fleet interactions with transit, commercial, or emergency vehicle drivers) are covered by separate objects. |
| ITS Roadway Equipment | Field | 'ITS Roadway Equipment' represents the ITS equipment that is distributed on and along the roadway that monitors and controls traffic and monitors and manages the roadway. This physical object includes traffic detectors, environmental sensors, traffic signals, highway advisory radios, dynamic message signs, CCTV cameras and video image processing systems, grade crossing warning systems, and ramp metering systems. Lane management systems and barrier systems that control access to transportation infrastructure such as roadways, bridges and tunnels are also included. This object also provides environmental monitoring including sensors that measure road conditions, surface weather, and vehicle emissions. Work zone systems including work zone surveillance, traffic control, driver warning, and work crew safety systems are also included. |
| MMV User | Personal | The 'MMV User' represents the person that operates a micromobility vehicle (MMV). Included are cyclists and operators of other low-powered mobility devices such as e-scooters, powered wheelchairs, and power assisted bicycles where the interactions are not particular to the type of vehicle (e.g., interactions supporting vehicle safety applications). The MMV User participates in ITS services that support safe, shared use of the transportation network by motorized and non-motorized transportation modes. Representing those using non-motorized travel modes, and in particular bicyclists that sometimes share motor vehicle lanes, these MMV users provide input (e.g. a call signal requesting right of way at an intersection) and may be detected by ITS services to improve safety. The MMV User originates requests and receives information that reflects the interactions which might be useful to all users, regardless of vehicle type. |
| Other ITS Roadway Equipment | Field | Representing another set of ITS Roadway Equipment, 'Other ITS Roadway Equipment' supports 'field device' to 'field device' communication and coordination, and provides a source and destination for information that may be exchanged between ITS Roadway Equipment. The interface enables direct coordination between field equipment. Examples include the direct interface between sensors and other roadway devices (e.g., Dynamic Message Signs) and the direct interface between roadway devices (e.g., between a Signal System Master and Signal System Local equipment) or a connection between an arterial signal system master and a ramp meter controller. |
| Pedestrian | Personal | The 'Pedestrian' represents a person traveling on foot. Pedestrians participate in ITS services that support safe, shared use of the transportation network. Included are visually impaired travelers who travel through portions of the transportation network and interact with ITS systems. They provide input (e.g. a call signal requesting right of way at an intersection) and may be detected by ITS services to improve safety |
| Traffic Management Center | Center | The 'Traffic Management Center' monitors and controls traffic and the road network. It represents centers that manage a broad range of transportation facilities including freeway systems, rural and suburban highway systems, and urban and suburban traffic control systems. It communicates with ITS Roadway Equipment and Connected Vehicle Roadside Equipment (RSE) to monitor and manage traffic flow and monitor the condition of the roadway, surrounding environmental conditions, and field equipment status. It manages traffic and transportation resources to support allied agencies in responding to, and recovering from, incidents ranging from minor traffic incidents through major disasters. |
| Traffic Operations Personnel | Center | 'Traffic Operations Personnel' represents the people that operate a traffic management center. These personnel interact with traffic control systems, traffic surveillance systems, incident management systems, work zone management systems, and travel demand management systems. They provide operator data and command inputs to direct system operations to varying degrees depending on the type of system and the deployment scenario. |
| Vehicle | Vehicle | This 'Vehicle' physical object is used to model core capabilities that are common to more than one type of Vehicle. It provides the vehicle-based general sensory, processing, storage, and communications functions that support efficient, safe, and convenient travel. Many of these capabilities (e.g., see the Vehicle Safety service packages) apply to all vehicle types including personal vehicles (including motorcycles), commercial vehicles, emergency vehicles, transit vehicles, and maintenance vehicles. From this perspective, the Vehicle includes the common interfaces and functions that apply to all motorized vehicles. The radio(s) supporting V2V and V2I communications are a key component of the Vehicle. Both one-way and two-way communications options support a spectrum of information services from basic broadcast to advanced personalized information services. Advanced sensors, processors, enhanced driver interfaces, and actuators complement the driver information services so that, in addition to making informed mode and route selections, the driver travels these routes in a safer and more consistent manner. This physical object supports all six levels of driving automation as defined in SAE J3016. Initial collision avoidance functions provide 'vigilant co-pilot' driver warning capabilities. More advanced functions assume limited control of the vehicle to maintain lane position and safe headways. In the most advanced implementations, this Physical Object supports full automation of all aspects of the driving task, aided by communications with other vehicles in the vicinity and in coordination with supporting infrastructure subsystems. |
| Vehicle Characteristics | Vehicle | 'Vehicle Characteristics' represents the external view of individual vehicles of any class from cars and light trucks up to large commercial vehicles and down to micromobility vehicles (MMVs). It includes vehicle physical characteristics such as height, width, length, weight, and other properties (e.g., magnetic properties, number of axles, occupants, emissions) of individual vehicles that can be sensed and measured or classified. This physical object represents the physical properties of vehicles that can be sensed by vehicle-based or infrastructure-based sensors to support vehicle automation and traffic sensor systems. The analog properties provided by this terminator represent the sensor inputs that are used to detect and assess vehicle(s) within the sensor's range to support safe AV operation and/or responsive and safe traffic management. |
Includes Functional Objects:
| Functional Object | Description | Physical Object |
|---|---|---|
| Roadway Field Management Station Operation | 'Roadway Field Management Station Operation' supports direct communications between field management stations and the local field equipment under their control. | ITS Roadway Equipment |
| Roadway Signal Control | 'Roadway Signal Control' includes the field elements that monitor and control signalized intersections. It includes the traffic signal controllers, detectors, conflict monitors, signal heads, and other ancillary equipment that supports traffic signal control. It also includes field masters, and equipment that supports communications with a central monitoring and/or control system, as applicable. The communications link supports upload and download of signal timings and other parameters and reporting of current intersection status. It represents the field equipment used in all levels of traffic signal control from basic actuated systems that operate on fixed timing plans through adaptive systems. It also supports all signalized intersection configurations, including those that accommodate pedestrians. In advanced, future implementations, environmental data may be monitored and used to support dilemma zone processing and other aspects of signal control that are sensitive to local environmental conditions. | ITS Roadway Equipment |
| Roadway Surveillance | 'Roadway Basic Surveillance' monitors traffic conditions using fixed equipment such as loop detectors, CCTV cameras, , RADARs and LIDARs. | ITS Roadway Equipment |
| RSE Intersection Management | 'RSE Intersection Management' uses short range communications to support connected vehicle applications that manage signalized intersections. It communicates with approaching vehicles and ITS infrastructure (e.g., the traffic signal controller) to enhance traffic signal operations. Coordination with the ITS infrastructure also supports conflict monitoring to ensure the RSE output and traffic signal control output are consistent and degrade in a fail safe manner. This object also has the required functionalities for optimizing Signal Phase and Timing (SPaT), sending necessary commands to traffic signal controller to execute the optimized SPaT, and updating SPaT in real-time. | Connected Vehicle Roadside Equipment |
| RSE Situation Monitoring | 'RSE Situation Monitoring' is a general functional object that supports collection of traffic, environmental, and emissions data from passing vehicles. The data is collected, filtered, and forwarded based on parameters provided by the back office. Parameters are provided to passing vehicles that are equipped to collect and send situation data to the infrastructure in snapshots. In addition, this object collects current status information from local field devices including intersection status, sensor data, and signage data, providing complete, configurable monitoring of the situation for the local transportation system in the vicinity of the RSE. | Connected Vehicle Roadside Equipment |
| RSE Traffic Monitoring | 'RSE Traffic Monitoring' monitors the basic safety messages that are shared between connected vehicles, correlates multiple messages received from connected vehicles, and distills this data into traffic flow measures that can be used to manage the network in combination with or in lieu of traffic data collected by infrastructure-based sensors. As connected vehicle penetration rates increase, the measures provided by this application can expand beyond vehicle speeds that are directly reported by vehicles to include estimated volume, occupancy, and other measures. This object also supports incident detection by monitoring for changes in speed and vehicle control events that indicate a potential incident. | Connected Vehicle Roadside Equipment |
| TMC Basic Surveillance | 'TMC Basic Surveillance' remotely monitors and controls traffic sensor systems and surveillance (e.g., CCTV) equipment, and collects, processes and stores the collected traffic data. Current traffic information and other real-time transportation information is also collected from other centers. The collected information is provided to traffic operations personnel and made available to other centers. | Traffic Management Center |
| TMC Roadway Equipment Monitoring | 'TMC Roadway Equipment Monitoring' monitors the operational status of field equipment and detects failures. It presents field equipment status to Traffic Operations Personnel and reports failures to the Maintenance and Construction Management Center. It tracks the repair or replacement of the failed equipment. The entire range of ITS field equipment may be monitored including sensors (traffic, infrastructure, environmental, security, speed, etc.) and devices (highway advisory radio, dynamic message signs, automated roadway treatment systems, barrier and safeguard systems, cameras, traffic signals and override equipment, ramp meters, beacons, security surveillance equipment, etc.). | Traffic Management Center |
| TMC Signal Control | 'TMC Signal Control' provides the capability for traffic managers to monitor and manage the traffic flow at signalized intersections. This capability includes analyzing and reducing the collected data from traffic surveillance equipment and developing and implementing control plans for signalized intersections. Control plans may be developed and implemented that coordinate signals at many intersections under the domain of a single Traffic Management Center and are responsive to traffic conditions and adapt to support incidents, preemption and priority requests, pedestrian crossing calls, etc. This may include adaptive traffic control systems (ATCS) that adjust signal timings based on traffic conditions, demand, and system capacity. It also supports all signalized intersection configurations, including those that accommodate pedestrians. | Traffic Management Center |
| Vehicle Basic Safety Communication | 'Vehicle Basic Safety Communication' exchanges current vehicle characteristics, location, and motion (including past and intended maneuver) information with other vehicles in the vicinity and the infrastructure, uses that information to calculate vehicle paths, and warns the driver when the potential for an impending collision is detected. If available, map data is used to filter and interpret the relative location and motion of vehicles in the vicinity. Information from on-board sensors (e.g., radars and image processing) are also used, if available, in combination with the V2V communications to detect non-equipped vehicles and corroborate connected vehicle data. This object represents a broad range of implementations ranging from basic Vehicle Awareness Devices that only broadcast vehicle location and motion and provide no driver warnings to advanced integrated safety systems that coordinate maneuvers and may, in addition to warning the driver, provide collision warning information to support automated control functions that can support control intervention. This object can also support broadcasting other vehicle information required for passing through a specific roadway segment such as variables that describe vehicle's characteristics and parameters, driver's preferences in terms of vehicle motion and behavior, etc. | Vehicle |
| Vehicle Intersection Movement | 'Vehicle Intersection Movement' uses short-range wireless communications to monitor other connected vehicles at intersections and support the safe movement of the vehicle through the intersection by receiving and processing signal phase and timing messages from the intersection. Driver warnings are provided and the application may also optionally take control of the vehicle to avoid collisions, in coordination with Vehicle Control Automation. The application will also notify the infrastructure and other vehicles if it detects an unsafe infringement on the intersection. | Vehicle |
| Vehicle Situation Data Monitoring | 'Vehicle Situation Data Monitoring' is the highest-level representation of the functionality required to collect traffic and environmental situation data by monitoring and storing the experience of the vehicle as it travels through the road network. Collected data is aggregated into snapshots that are reported when communications is available and with flow control based on parameters provided by the infrastructure. Note that this functional object supports collection of data for areas remote from RSEs or other communications infrastructure. | Vehicle |
Includes Information Flows:
| Information Flow | Description |
|---|---|
| conflict monitor status | A control flow that supports failsafe operation in the event that a conflict is detected that requires the RSE to enter a failsafe operating mode for intersection management. Analogous to a traffic signal conflict monitor, this flow is issued when differences are detected between information provided to the vehicle for in-vehicle display and information displayed by field devices. It contains the details of differences that were found. |
| crossing call | Non-motorized user request to cross the roadway. This is an overt request from a pedestrian, micromobility vehicle user (e.g., cyclist), or other vulnerable road user. This overt request may be a physical button push or hovering or gesturing in the vicinity of the button that supports contactless activation. |
| crossing permission | Information provided to guide and warn pedestrians, micromobility vehicle users (e.g., cyclists), and other crosswalk users. It includes crossing request acknowledgment, current crossing permission, crossing time remaining, and real-time warnings of safety threats. |
| driver information | Regulatory, warning, guidance, and other information provided to the driver to support safe and efficient vehicle operation. |
| driver input | Driver input to the vehicle on-board equipment including configuration data, settings and preferences, interactive requests, and control commands. |
| driver updates | Information provided to the driver including visual displays, audible information and warnings, and haptic feedback. The updates inform the driver about current conditions, potential hazards, and the current status of vehicle on-board equipment. |
| intersection control status | Status data provided by the traffic signal controller including phase information, alarm status, and priority/preempt status. |
| intersection geometry | The physical geometry of an intersection covering the location and width of each approaching lane, egress lane, and valid paths between approaches and egresses. This flow also defines the location of stop lines, cross walks, specific traffic law restrictions for the intersection (e.g., turning movement restrictions), and other elements that support calculation of a safe and legal vehicle path through the intersection. |
| intersection management application info | Intersection and device configuration data, including intersection geometry, and warning parameters and thresholds. This flow also supports remote control of the application so the application can be taken offline, reset, or restarted. |
| intersection management application status | Infrastructure application status including current operational state and status of the field device and a log of operations. |
| intersection status | Current signal phase and timing information for all lanes at a signalized intersection. This flow identifies active lanes and lanes that are being stopped and specifies the length of time that the current state will persist for each lane. It also identifies signal priority and preemption status and pedestrian crossing status information where applicable. It may also include future signal phase and timing information. |
| intersection status monitoring | Current signal phase and timing information for all lanes at a signalized intersection. This flow represents monitoring of communications by a receiver at the intersection to support monitoring for conflicts between actual signal states and RSE communications about those states. |
| right-of-way request coordination | The direct flow of information between field equipment. This includes notification of crossing calls from pedestrians and other vulnerable road users and requests for signal prioritization or preemption, and any other request for right-of-way at an intersection. The status of the request is also shared. For vulnerable road users, this includes information provided to guide and warn vulnerable road users at crossings including crossing permission status and crossing time remaining. |
| right-of-way request notification | Notice that a request has occurred for signal prioritization, signal preemption, pedestrian call, multi-modal crossing activation, or other source for right-of-way. |
| signal control commands | Control of traffic signal controllers or field masters including clock synchronization. |
| signal control coordination | The direct flow of information between field equipment. This includes configuration and control of traffic signal controllers or field masters. Configuration data and operational status of traffic signal control equipment including operating condition and current indications are returned. |
| signal control device configuration | Data used to configure traffic signal control equipment including local controllers and system masters. |
| signal control plans | Traffic signal timing parameters including minimum green time and interval durations for basic operation and cycle length, splits, offset, phase sequence, etc. for coordinated systems. |
| signal control status | Operational and status data of traffic signal control equipment including operating condition and current indications. |
| signal fault data | Faults reported by traffic signal control equipment. |
| signal service request | A call for service or extension for a signal control phase that is issued by the RSE for connected vehicles approaching an intersection and/or pedestrians at a crosswalk. This flow identifies the desired phase and service time. |
| signal system configuration | Data used to configure traffic signal systems including configuring control sections and mode of operation (time based or traffic responsive). |
| traffic detector control | Information used to configure and control traffic detector systems such as inductive loop detectors and machine vision sensors. |
| traffic detector coordination | The direct flow of information between field equipment. This includes information used to configure and control traffic detector systems such as inductive loop detectors and machine vision sensors Raw and/or processed traffic detector data is returned that allows derivation of traffic flow variables (e.g., speed, volume, and density measures) and associated information (e.g., congestion, potential incidents). This flow includes the traffic data and the operational status of the traffic detectors |
| traffic detector data | Raw and/or processed traffic detector data which allows derivation of traffic flow variables (e.g., speed, volume, and density measures) and associated information (e.g., congestion, potential incidents). This flow includes the traffic data and the operational status of the traffic detectors |
| traffic operator data | Presentation of traffic operations data to the operator including traffic conditions, current operating status of field equipment, maintenance activity status, incident status, video images, security alerts, emergency response plan updates and other information. This data keeps the operator appraised of current road network status, provides feedback to the operator as traffic control actions are implemented, provides transportation security inputs, and supports review of historical data and preparation for future traffic operations activities. |
| traffic operator input | User input from traffic operations personnel including requests for information, configuration changes, commands to adjust current traffic control strategies (e.g., adjust signal timing plans, change DMS messages), and other traffic operations data entry. |
| traffic situation data | Current, aggregate traffic data collected from connected vehicles. It includes raw and/or processed reported vehicle speeds, counts, and other derived measures. Raw and/or filtered vehicle control events may also be included to support incident detection. This flow represents information collected from a single probe data collection point in the road network (e.g., a CVRSE or a MEC). |
| vehicle characteristics | The physical or visible characteristics of individual vehicles that can be used to detect, classify, and monitor vehicles and imaged to uniquely identify vehicles and characterize their performance (e.g., speed, occupants, emissions). |
| vehicle location and motion for surveillance | Data describing the vehicle's location in three dimensions, heading, speed, acceleration, braking status, and size. This flow represents monitoring of basic safety data ('vehicle location and motion') broadcast by passing connected vehicles for use in vehicle detection and traffic monitoring applications. |
| vehicle situation data | This flow represents vehicle snapshots that may be provided by the vehicle to support traffic and environmental conditions monitoring. Snapshots are collected by the vehicle for specific events (e.g., when a sensor exceeds a threshold) or periodically and reported based on control parameters when communications is available. Traffic-related data includes snapshots of measured speed and heading and events including starts and stops, speed changes, and other vehicle control events. Environmental data may include measured air temperature, exterior light status, wiper status, sun sensor status, rain sensor status, traction control status, anti-lock brake status, and other collected vehicle system status and sensor information. The collected data is reported along with the location, heading, and time that the data was collected. |
| vehicle situation data parameters | A request for vehicle situation data that includes parameters used to control the data that is reported and the flow of data reported by the vehicle. This flow identifies the type of data/snapshots that are requested and reporting parameters such as snapshot frequency, filtering criteria (data thresholds for reporting), and reporting interval. |
Goals and Objectives
Associated Planning Factors and Goals
| Planning Factor | Goal |
|---|
Associated Objective Categories 
| Objective Category |
|---|
Associated Objectives and Performance Measures 
| Objective | Performance Measure |
|---|

Needs and Requirements
| Need | Functional Object | Requirement | ||
|---|---|---|---|---|
Related Sources
| Document Name | Version | Publication Date |
|---|---|---|
| None |
Security
In order to participate in this service package, each physical object should meet or exceed the following security levels.
| Physical Object Security | ||||
|---|---|---|---|---|
| Physical Object | Confidentiality | Integrity | Availability | Security Class |
| Connected Vehicle Roadside Equipment | Moderate | High | Moderate | Class 3 |
| ITS Roadway Equipment | Moderate | High | Moderate | Class 3 |
| Other ITS Roadway Equipment | Moderate | Moderate | Moderate | Class 2 |
| Traffic Management Center | Moderate | High | Moderate | Class 3 |
| Vehicle | Moderate | Moderate | Moderate | Class 2 |
| Vehicle Characteristics | ||||
In order to participate in this service package, each information flow triple should meet or exceed the following security levels.
| Information Flow Security | |||||
|---|---|---|---|---|---|
| Source | Destination | Information Flow | Confidentiality | Integrity | Availability |
| Basis | Basis | Basis | |||
| Connected Vehicle Roadside Equipment | ITS Roadway Equipment | intersection status monitoring | Moderate | High | Moderate |
| This data is intentionally transmitted to everyone via a While this information can be ascertained by examining signal states, all communications between field infrastructure should be protected from viewing to prevent attackers from analyzing traffic and developing attack methods. | If this is compromised, the RSE could send incorrect data to the Roadway Equipment. Since the data contained herein directly affects human safety, the Roadway Equipment may react to tell the RSE it is in conflict, which in turn may result in the RSE modifying or disabling its outputs. DISC THEA: info needs to be accurate and should not be tampered so the ITS RE has correct SPaT info for all lanes to be able to detect conflicts and support failsafe operating mode. DISC: THEA belives this may be HIGH for ISIG. NYC also believes this to be HIGH for PED-SIG. | A delay in reporting this may allow the RSE to distribute faulty information, but that information is contradicted by the signal state. Since there are multiple pathways for the information to be obtained, this is not ‘High. | |||
| Connected Vehicle Roadside Equipment | ITS Roadway Equipment | signal service request | Moderate | Moderate | Low |
| info is not confidential and could be exposed with little harm to participants; however, all communications between field infrastructure should be protected from viewing to prevent attackers from analyzing traffic and developing attack methods. | requests should be accurate and not tampered with, otherwise incorrect or malicious requests could be granted which could lead to delays | requests should be timely and available immediately but availability cannot be guaranteed over a wireless medium; also worst case scenario is the vehicle or pedestrian has to wait for the appropriate signal | |||
| Connected Vehicle Roadside Equipment | ITS Roadway Equipment | traffic situation data | Moderate | Moderate | Moderate |
| Aggregated messages may have more privacy implications than individual ones, especially if an attacker can attack more than one RSE-to-TMC connection at once. | This information is used to help with incident detection. It should be verified to ensure that it is not incorrectly influencing this.THEA: only limited adverse effect if raw/processed connected vehicle data is bad/compromised; could be LOW for ISIG | This information is used as supplemental information. It should operate correctly if not every single message is received. THEA: only limited adverse effect if info is not timely/readily available, could be LOW for ISIG | |||
| Connected Vehicle Roadside Equipment | Traffic Management Center | intersection management application status | Moderate | Moderate | Low |
| This information could be of interest to a malicious individual who is attempting to determine the best way to accomplish a crime. As such it would be best to not make it easily accessible. May be LOW in some cases. | If this is compromised, it could send unnecessary maintenance workers, or worse report plausible data that is erroneous. From THEA: should be able to cope with some bad information on the status and record of alerts/warnings; aggregate info; however could cause appearance of excessive traffic violations or unnecessary maintenance caused if data is compromised (operational state, status, log); should not affect the application functionality | Incident status information should be presented in timely fashion as large scale mobility and safety issues are related. There are other mechanisms for reporting this information however, thus MODERATE. From THEA: Only limited adverse effect of info is not timely/readily available | |||
| Connected Vehicle Roadside Equipment | Traffic Management Center | traffic situation data | Moderate | Moderate | Low |
| Aggregated messages may have more privacy implications than individual ones, especially if an attacker can attack more than one RSE-to-TMC connection at once. | only limited adverse effect if raw/processed connected vehicle data is bad/compromised; DISC: NYC believes this to be MODERATE: As investigation might be triggered if RF quality is reported as low, this data should be trusted. RES: Agree wih NYC. | only limited adverse effect of info is not timely/readily available. NYC: This data is purely for statistical purposes so low availability does not harm the [RSE RF Monitoring] application. | |||
| Connected Vehicle Roadside Equipment | Vehicle | intersection geometry | Low | High | Moderate |
| Map data intended for general use by any C-ITS component than needs it. No information here includes PII or anything else that, if viewed by someone other than the participant, would lead to harm. | Map data is used for a host of application purposes. This widespread use means that any corruption in the data has a widespread and far reaching effect. | Occasional outages of this flow will delay updates and lead to a loss of accurate function of some applications. Depending on the application this could be HIGH. | |||
| Connected Vehicle Roadside Equipment | Vehicle | intersection status | Not Applicable | High | Moderate |
| This data is intended for all vehicles in the immediate area of the sender. | If this is compromised, the Vehicle OBE will receive messages that are inconsistent with what the traffic signals are displaying. This could lead to confusion and reduce the ability of the application to provide value. | If this is down, the Vehicle OBE doesn’t get the information it needs to stay in synch with the actual signal state, reducing or eliminating the value add from having this application. We assume that the Vehicle OBE will detect a lack of availability and choose not to send out-of-date information, so a failure of availability cannot have worse consequences than a failure of integrity which we have previously assessed at MEDIUM. | |||
| Connected Vehicle Roadside Equipment | Vehicle | vehicle situation data parameters | Low | Moderate | Moderate |
| This isn't exactly a control flow, more like a 'suggestion flow', as the vehicle will always decide what to send. Probably no need for obfuscation. | Info should be accurate and should not be tampered so that the vehicle only discloses the correctly requested data | Parameters should be timely and readily available, but would not have severe/catastrophic consequences if not | |||
| Driver | Vehicle | driver input | Moderate | High | High |
| Data included in this flow may include origin and destination information, which should be protected from other's viewing as it may compromise the driver's privacy. | Commands from from the driver to the vehicle must be correct or the vehicle may behave in an unpredictable and possibly unsafe manner | Commands must always be able to be given or the driver has no control. | |||
| ITS Roadway Equipment | Connected Vehicle Roadside Equipment | conflict monitor status | Moderate | High | Moderate |
| Trains arriving should be visible, viewable and certainly not concealed. Reception of this information may indicate position or intended position of the recipient, which is slightly sensitive; thus LOW and not N/A is typically justified. However, all communications between field infrastructure should be protected from viewing to prevent attackers from analyzing traffic and developing attack methods. | If this is compromised, it could send incorrect data to the RSE. Since the data contained herein directly affects human safety, the RSE may react to modify its outputs, at the least disabling related outputs. if compromised, the ITS RE may not be able to support failsafe operating mode in the event of a conflict between the ITS RE and RSE. May not be ‘High’ because the signal state is also present. From NYC: This flow tells the RSE that the traffic controller is in a failed state – typically flashing signals not timing. | A delay in reporting this may allow the RSE to distribute faulty information, but that information is contradicted by the signal state. Since there are multiple pathways for the information to be obtained, this is not ‘High.’ | |||
| ITS Roadway Equipment | Connected Vehicle Roadside Equipment | intersection control status | Moderate | High | Moderate |
| This data is intentionally transmitted to everyone via a While this information is broadcast and can also be determined via other visual indicators, all communications between field infrastructure should be protected from viewing to prevent attackers from analyzing traffic and developing attack methods. | If this is compromised, the Roadway Equipment and Roadside Equipment will be sending messages that are inconsistent with each other, leading to confusion and possible accidents. | If this is down, the RSE doesn’t get the information it needs to stay in synch with the actual signal state, reducing or eliminating the value add from having this application. The RSE must detect a lack of availability and choose not to send out-of-date information, so a failure of availability could be interpreted as having the same value as Integrity. However, this data is semi-predictable and there are other indicators (such as the lights themselves) of the intersection status. From NYC, who believe this should be HIGH for some applications: If this is down, the RSE doesn’t get the information it needs to stay in synch with the actual signal state, reducing or eliminating the value add from having this application. The RSE must detect a lack of availability and choose not to send out-of-date information, so a failure of availability cannot have worse consequences than a failure of integrity which we have previously assessed at HIGH. | |||
| ITS Roadway Equipment | Driver | driver information | Not Applicable | High | Moderate |
| This data is sent to all drivers and is also directly observable, by design. | This is the primary signal trusted by the driver to decide whether to go through the intersection and what speed to go through the intersection at; if it’s wrong, accidents could happen. | If the lights are out you have to get a policeman to direct traffic – expensive and inefficient and may cause a cascading effect due to lack of coordination with other intersections. | |||
| ITS Roadway Equipment | MMV User | crossing permission | Not Applicable | High | Low |
| This data is intentionally transmitted to everyone via a broadcast. | Although pedestrians have a responsibility to make sure the road is safe before they cross, they may react instinctively to incorrect information and be led to cross at unsafe times if they get incorrect information. Also, if the traffic signals are wrong and an accident happens, the pedestrian involved could sue, causing financial loss and other undesirable outcomes. | It is easy to tell whether this information flow is available and pedestrians are used to using crosswalks that do not provide this service. | |||
| ITS Roadway Equipment | Other ITS Roadway Equipment | right-of-way request coordination | Moderate | Moderate | Moderate |
| Any control flow has some confidentiality requirement, as observation of the flow may enable an attacker to analyze and learn how to assume control. MODERATE for most flows as the potential damage is likely contained, though anything that could have a significant safety impact may be assigned HIGH. | Since this directly impacts device control, we consider it the same as a control flow. Control flows, even for seemingly innocent devices, should have MODERATE integrity at minimum, just to guarantee that intended control messages are received. Incorrect, corrupted, intercepted and modified control messages can or will result in target field devices not behaving according to operator intent. The severity of this depends on the type of device, which is why some devices are set MODERATE and some HIGH. | Since this directly impacts device control, we consider it the same as a control flow. Control flow availability is related to the criticality of being able to remotely control the device. For most devices, this is MODERATE. For purely passive devices with no incident relationship, this will be LOW. All devices should have default modes that enable them to operate without backhaul connectivity, so no device warrants a HIGH. | |||
| ITS Roadway Equipment | Other ITS Roadway Equipment | signal control coordination | Moderate | Moderate | Moderate |
| Any control flow has some confidentiality requirement, as observation of the flow may enable an attacker to analyze and learn how to assume control. MODERATE for most flows as the potential damage is likely contained, though anything that could have a significant safety impact may be assigned HIGH. | Since this directly impacts device control, we consider it the same as a control flow. Control flows, even for seemingly innocent devices, should have MODERATE integrity at minimum, just to guarantee that intended control messages are received. Incorrect, corrupted, intercepted and modified control messages can or will result in target field devices not behaving according to operator intent. The severity of this depends on the type of device, which is why some devices are set MODERATE and some HIGH. | Since this directly impacts device control, we consider it the same as a control flow. Control flow availability is related to the criticality of being able to remotely control the device. For most devices, this is MODERATE. For purely passive devices with no incident relationship, this will be LOW. All devices should have default modes that enable them to operate without backhaul connectivity, so no device warrants a HIGH. | |||
| ITS Roadway Equipment | Other ITS Roadway Equipment | traffic detector coordination | Moderate | Moderate | Low |
| Any control flow has some confidentiality requirement, as observation of the flow may enable an attacker to analyze and learn how to assume control. MODERATE for most flows as the potential damage is likely contained, though anything that could have a significant safety impact may be assigned HIGH. | Since this directly impacts device control, we consider it the same as a control flow. Control flows, even for seemingly innocent devices, should have MODERATE integrity at minimum, just to guarantee that intended control messages are received. Incorrect, corrupted, intercepted and modified control messages can or will result in target field devices not behaving according to operator intent. The severity of this depends on the type of device, which is why some devices are set MODERATE and some HIGH. | Since this directly impacts device control, we consider it the same as a control flow. Control flow availability is related to the criticality of being able to remotely control the device. For most devices, this is MODERATE. For purely passive devices with no incident relationship, this will be LOW. All devices should have default modes that enable them to operate without backhaul connectivity, so no device warrants a HIGH. | |||
| ITS Roadway Equipment | Pedestrian | crossing permission | Not Applicable | High | Low |
| This data is intentionally transmitted to everyone via a broadcast. | Although pedestrians have a responsibility to make sure the road is safe before they cross, they may react instinctively to incorrect information and be led to cross at unsafe times if they get incorrect information. Also, if the traffic signals are wrong and an accident happens, the pedestrian involved could sue, causing financial loss and other undesirable outcomes. | It is easy to tell whether this information flow is available and pedestrians are used to using crosswalks that do not provide this service. | |||
| ITS Roadway Equipment | Traffic Management Center | right-of-way request notification | Low | Moderate | Moderate |
| This can be reasonably guessed based on observing the ITS RE’s environment. It is obvious when a bus approaches an intersection. | Invalid messages could lead to an unauthorized user gaining signal priority at an intersection. This could also be used to delay traffic, which could lead to a financial impact on the community. However, the traffic signal will have controls in place to ensure that it does not display an illegal configuration (such as green in every direction). | Even if all of the Right-of-way Requests are not passed along from an ITS RE, the intersection will still operate as normal. There are other existing methods to assist a right-of-way requesting vehicle safely traveling through an intersection, such as lights and sirens, which prevent this from being a HIGH. DISC: THEA and NYC believe this to be LOW: "not necessary for the app to work; can cope with not having immediately available data" | |||
| ITS Roadway Equipment | Traffic Management Center | signal control status | Low | High | Moderate |
| The current conditions of an ITS RE are completely observable, by design. | This influences the TMC response to a right-of-way request. It should be as accurate as the right-of-way request themselves. For some applications (ISIG) this need only be moderate. Per THEA: info needs to be accurate and should not be tampered to enable effective monitoring and control by the TMC. DISC: THEA believes this to be MODERATE: "info needs to be accurate and should not be tampered to enable effective monitoring and control by the TMC; should be as accurate as the right of way request". NYC:TMC doesn’t play an active role in this application, i.e. even if the information contained in this flow were incorrect, it is unlikely to affect the outcome of this application one way or the other. On some applications NYC has this MODERATE though. RES: This value can obviously change a lot depending on the application context. | The TMC will need the current status of the ITS RE in order to make an educated decision. If it is unavailable, the system is unable to operate. However, a few missed messages will not have a catastrophic impact. From NYC: TMC doesn’t play an active role in this application, i.e. even if it is unavailable, it is unlikely to affect the outcome of this application one way or the other. RES: This value can change a lot depending on the application context. | |||
| ITS Roadway Equipment | Traffic Management Center | signal fault data | Low | High | Moderate |
| The current conditions of an ITS RE are completely observable, by design. | Control flows, even for seemingly innocent devices, should have MODERATE integrity at minimum, just to guarantee that intended control messages are received. Incorrect, corrupted, intercepted and modified control messages can or will result in target field devices not behaving according to operator intent. The severity of this depends on the type of device, which is why some devices are set MODERATE and some HIGH. | Control flow availability is related to the criticality of being able to remotely control the device. For most devices, this is MODERATE. | |||
| ITS Roadway Equipment | Traffic Management Center | traffic detector data | Low | Moderate | Moderate |
| No impact if someone sees the data | Some minimal guarantee of data integrity is necessary for all C-ITS flows. THEA believes this to be LOW.only limited adverse effect if raw/processed traffic detector data is bad/compromised; DISC: WYO believes this to be HIGH | Only limited adverse effect of info is not timely/readily available, however without this information it will be difficult to perform traffic management activities, thus MODERATE. If not used for management, may be LOW. | |||
| MMV User | ITS Roadway Equipment | crossing call | Not Applicable | High | Low |
| The "Not Applicable" group includes information flows that do not actually carry information; for example, flows that represent the physical environment. | Although pedestrians have a responsibility to make sure the road is safe before they cross, and should ensure that they are detected by pedestrian detection systems, they may not always be detected and be led to cross at unsafe times if the ITS RE obtains incorrect information. | It is easy to tell whether this information flow is available and pedestrians are used to using crosswalks that do not provide this service. | |||
| Other ITS Roadway Equipment | ITS Roadway Equipment | right-of-way request coordination | Moderate | Moderate | Moderate |
| Any control flow has some confidentiality requirement, as observation of the flow may enable an attacker to analyze and learn how to assume control. MODERATE for most flows as the potential damage is likely contained, though anything that could have a significant safety impact may be assigned HIGH. | Since this directly impacts device control, we consider it the same as a control flow. Control flows, even for seemingly innocent devices, should have MODERATE integrity at minimum, just to guarantee that intended control messages are received. Incorrect, corrupted, intercepted and modified control messages can or will result in target field devices not behaving according to operator intent. The severity of this depends on the type of device, which is why some devices are set MODERATE and some HIGH. | Since this directly impacts device control, we consider it the same as a control flow. Control flow availability is related to the criticality of being able to remotely control the device. For most devices, this is MODERATE. For purely passive devices with no incident relationship, this will be LOW. All devices should have default modes that enable them to operate without backhaul connectivity, so no device warrants a HIGH. | |||
| Other ITS Roadway Equipment | ITS Roadway Equipment | signal control coordination | Moderate | Moderate | Moderate |
| Any control flow has some confidentiality requirement, as observation of the flow may enable an attacker to analyze and learn how to assume control. MODERATE for most flows as the potential damage is likely contained, though anything that could have a significant safety impact may be assigned HIGH. | Since this directly impacts device control, we consider it the same as a control flow. Control flows, even for seemingly innocent devices, should have MODERATE integrity at minimum, just to guarantee that intended control messages are received. Incorrect, corrupted, intercepted and modified control messages can or will result in target field devices not behaving according to operator intent. The severity of this depends on the type of device, which is why some devices are set MODERATE and some HIGH. | Since this directly impacts device control, we consider it the same as a control flow. Control flow availability is related to the criticality of being able to remotely control the device. For most devices, this is MODERATE. For purely passive devices with no incident relationship, this will be LOW. All devices should have default modes that enable them to operate without backhaul connectivity, so no device warrants a HIGH. | |||
| Other ITS Roadway Equipment | ITS Roadway Equipment | traffic detector coordination | Moderate | Moderate | Low |
| Any control flow has some confidentiality requirement, as observation of the flow may enable an attacker to analyze and learn how to assume control. MODERATE for most flows as the potential damage is likely contained, though anything that could have a significant safety impact may be assigned HIGH. | Since this directly impacts device control, we consider it the same as a control flow. Control flows, even for seemingly innocent devices, should have MODERATE integrity at minimum, just to guarantee that intended control messages are received. Incorrect, corrupted, intercepted and modified control messages can or will result in target field devices not behaving according to operator intent. The severity of this depends on the type of device, which is why some devices are set MODERATE and some HIGH. | Since this directly impacts device control, we consider it the same as a control flow. Control flow availability is related to the criticality of being able to remotely control the device. For most devices, this is MODERATE. For purely passive devices with no incident relationship, this will be LOW. All devices should have default modes that enable them to operate without backhaul connectivity, so no device warrants a HIGH. | |||
| Pedestrian | ITS Roadway Equipment | crossing call | Not Applicable | High | Low |
| The "Not Applicable" group includes information flows that do not actually carry information; for example, flows that represent the physical environment. | Although pedestrians have a responsibility to make sure the road is safe before they cross, and should ensure that they are detected by pedestrian detection systems, they may not always be detected and be led to cross at unsafe times if the ITS RE obtains incorrect information. | It is easy to tell whether this information flow is available and pedestrians are used to using crosswalks that do not provide this service. | |||
| Traffic Management Center | Connected Vehicle Roadside Equipment | intersection management application info | Moderate | High | Low |
| Proprietary configuration data with warning parameters and thresholds. | should be accurate and not be tampered with; could enable outside control of application | This message is an indication of a potential hazard. If it isn’t received it increases the risk to other road users. If a vehicle is infringing on an intersection, it must report this. | |||
| Traffic Management Center | ITS Roadway Equipment | signal control commands | Moderate | High | Moderate |
| Control flows, even for seemingly innocent devices, should be kept confidential to minimize attack vectors. While an individual installation may not be particularly impacted by a cyberattack of its sensor network, another installation might be severely impacted, and different installations are likely to use similar methods, so compromising one leads to compromising all. DISC: NYC believes this to be LOW: "The result of this will be directly observable." | Invalid messages could lead to an unauthorized user gaining control of an intersection. This could also be used to bring traffic to a standstill, which could lead to a large financial impact on the community. DISC: NYC believes this to be MODERATE: The signal timing is critical to the intersection operation; incorrect signal timing can lead to significant congestion and unreliable operation; while unsafe operation is controlled by the cabinet monitoring system, attackers could “freeze” the signal or call a preemption. RES: This will vary depending on the application and implementation. | These messages are important to help with preemption and signal priority applications. Without them, these applications mayl not work. However, if these signals are not received, the ITS RE will continue to function using its default configuration. The TMC should have an acknowledgement of the receipt of a message. DISC: NYC blieves this to be LOW: TMC doesn’t play an active role in this application, i.e. even if it is unavailable, it is unlikely to affect the outcome of this application one way or the other. RES: This will vary depending on the application and implementation. | |||
| Traffic Management Center | ITS Roadway Equipment | signal control device configuration | Moderate | High | Moderate |
| Control flows, even for seemingly innocent devices, should be kept confidential to minimize attack vectors. While an individual installation may not be particularly impacted by a cyberattack of its sensor network, another installation might be severely impacted, and different installations are likely to use similar methods, so compromising one leads to compromising all. DISC: THEA believes this to be LOW: "encrypted, authenticated, proprietary; however will not cause harm if seen, traffic light information is visible." | Control flows, even for seemingly innocent devices, should have MODERATE integrity at minimum, just to guarantee that intended control messages are received. Incorrect, corrupted, intercepted and modified control messages can or will result in target field devices not behaving according to operator intent. The severity of this depends on the type of device, which is why some devices are set MODERATE and some HIGH. From THEA: proprietary info that should not be tampered with; includes local controllers and system masters; tampering with configurations could cause delays along with major safety issues | Control flow availability is related to the criticality of being able to remotely control the device. For most devices, this is MODERATE. For purely passive devices with no incident relationship, this will be LOW. All devices should have default modes that enable them to operate without backhaul connectivity, so no device warrants a HIGH. From THEA: should be timely and readily available; however, should be able to function using a default configuration | |||
| Traffic Management Center | ITS Roadway Equipment | signal control plans | Moderate | High | Moderate |
| Control flows, even for seemingly innocent devices, should be kept confidential to minimize attack vectors. While an individual installation may not be particularly impacted by a cyberattack of its sensor network, another installation might be severely impacted, and different installations are likely to use similar methods, so compromising one leads to compromising all. DISC: THEA believes this to be LOW: "encrypted, authenticated, proprietary; but the result is directly observable from traffic lights | Control flows, even for seemingly innocent devices, should have MODERATE integrity at minimum, just to guarantee that intended control messages are received. Incorrect, corrupted, intercepted and modified control messages can or will result in target field devices not behaving according to operator intent. The severity of this depends on the type of device, which is why some devices are set MODERATE and some HIGH. From THEA: proprietary info that should not be tampered with; tampering with these plans could cause delays along with major safety issues | Control flow availability is related to the criticality of being able to remotely control the device. For most devices, this is MODERATE. For purely passive devices with no incident relationship, this will be LOW. All devices should have default modes that enable them to operate without backhaul connectivity, so no device warrants a HIGH. From THEA: should be timely and readily available; coordinated with other systems; however, should be able to function using a default configuration | |||
| Traffic Management Center | ITS Roadway Equipment | signal system configuration | Low | High | Moderate |
| encrypted, authenticated, proprietary; however, the result is directly observable from traffic lights | proprietary info that should not be tampered with; data used to configure traffic signal systems; could cause significant delays and traffic issues if compromised | should be readily available; configurations can be time | |||
| Traffic Management Center | ITS Roadway Equipment | traffic detector control | Moderate | Moderate | Low |
| Control flows, even for seemingly innocent devices, should be kept confidential to minimize attack vectors. While an individual installation may not be particularly impacted by a cyberattack of its sensor network, another installation might be severely impacted, and different installations are likely to use similar methods, so compromising one leads to compromising all. DISC: THEA, WYO believe this to be LOW: encrypted, authenticated, proprietary; but should not cause severe damage if seen | Control flows, even for seemingly innocent devices, should have MODERATE integrity at minimum, just to guarantee that intended control messages are received. Incorrect, corrupted, intercepted and modified control messages can or will result in target field devices not behaving according to operator intent. The severity of this depends on the type of device, which is why some devices are set MODERATE and some HIGH.. From THEA: should be accurate and not be tampered with; could enable outside control of traffic sensors but should not cause severe harm, but could cause issues with traffic sensor data received and be detrimental to operations | Control flow availability is related to the criticality of being able to remotely control the device. For most devices, this is MODERATE. For purely passive devices with no incident relationship, this will be LOW. All devices should have default modes that enable them to operate without backhaul connectivity, so no device warrants a HIGH.. From THEA: want updates but delayed information will not be severe; should be able to operate from a previous/default control/config. DISC: WYO believes this to be MODERATE | |||
| Traffic Management Center | Traffic Operations Personnel | traffic operator data | Moderate | Moderate | Moderate |
| Backoffice operations flows should have minimal protection from casual viewing, as otherwise imposters could gain illicit control or information that should not be generally available. | Information presented to backoffice system operators must be consistent or the operator may perform actions that are not appropriate to the real situation. | The backoffice system operator should have access to system operation. If this interface is down then control is effectively lost, as without feedback from the system the operator has no way of knowing what is the correct action to take. | |||
| Traffic Operations Personnel | Traffic Management Center | traffic operator input | Moderate | High | High |
| Backoffice operations flows should have minimal protection from casual viewing, as otherwise imposters could gain illicit control or information that should not be generally available. | Backoffice operations flows should generally be correct and available as these are the primary interface between operators and system. | Backoffice operations flows should generally be correct and available as these are the primary interface between operators and system. | |||
| Vehicle | Connected Vehicle Roadside Equipment | vehicle location and motion for surveillance | Not Applicable | Moderate | Moderate |
| This is directly observable data; DISC: WYO believes this to be MODERATE | Incorrect information here could lead to the system not functioning properly. If they are unable to properly detect all vehicles crossing the border, it would lead to confusion. There are other factors, such as visual indicators, of vehicles crossing the border, which can be used to help mitigate contradicting information. DISC: THEA believes this should be HIGH: "BSM info needs to be accurate and should not be tampered with" WYO believes this to be HIGH | This information must be available in a timely manner for the system to act upon it. The system can operate correctly if some messages are missed, but overall a majority of them should be received.; WYO believes this to be LOW | |||
| Vehicle | Connected Vehicle Roadside Equipment | vehicle situation data | Moderate | Moderate | Low |
| Might be able to link multiple snapshots together and compromise some element of driver/traveler privacy. | Some minimal guarantee of data integrity is necessary for all C-ITS flows. DISC: THEA believes this to be LOW: data should be accurate and not tampered with but should be able to cope with some bad data in traffic/environmental condition monitoring; aggregate data | data should be timely and readily available, but limited adverse effect; aggregate data | |||
| Vehicle | Driver | driver updates | Not Applicable | Moderate | Moderate |
| This data is informing the driver about the safety of a nearby area. It should not contain anything sensitive, and does not matter if another person can observe it. | This is the information that is presented to the driver. If they receive incorrect information, they may act in an unsafe manner. However, there are other indicators that would alert them to any hazards, such as an oncoming vehicle or crossing safety lights. | If this information is not made available to the driver, then the system has not operated correctly. | |||
| Vehicle Characteristics | ITS Roadway Equipment | vehicle characteristics | |||
Standards
The following table lists the standards associated with physical objects in this service package. For standards related to interfaces, see the specific information flow triple pages. These pages can be accessed directly from the SVG diagram(s) located on the Physical tab, by clicking on each information flow line on the diagram.
| Name | Title | Physical Object |
|---|---|---|
| CTI 4001 RSU | Roadside Unit (RSU) Standard | Connected Vehicle Roadside Equipment |
| CTI 4501 CI Implementation Guide | Connected Intersections Implementation Guide | Connected Vehicle Roadside Equipment |
| ISO 15623 Fwd Collision Performance | Intelligent transport systems -- Forward vehicle collision warning systems -- Performance requirements and test procedures | Vehicle |
| ISO 24100 Probe Vehicle Data Protection | Intelligent transport systems -- Basic principles for personal data protection in probe vehicle information services | Traffic Management Center |
| ITE 5201 ATC | Advanced Transportation Controller | ITS Roadway Equipment |
| ITE 5202 ATC Model 2070 | Model 2070 Controller Standard | ITS Roadway Equipment |
| ITE 5301 ATC ITS Cabinet | Intelligent Transportation System Standard Specification for Roadside Cabinets | ITS Roadway Equipment |
| ITE 5401 ATC API | Application Programming Interface Standard for the Advanced Transportation Controller | ITS Roadway Equipment |
| NEMA TS 8 Cyber and Physical Security | Cyber and Physical Security for Intelligent Transportation Systems | ITS Roadway Equipment |
| Traffic Management Center | ||
| NEMA TS2 Traffic Controller Assemblies | Traffic Controller Assemblies with NTCIP Requirements | ITS Roadway Equipment |
| SAE J3361 Antenna requirements | V2X Antenna Coverage and Test Requirements for US FHWA Class 1 and Class 3-13 Class Vehicles | Vehicle |
| SAE J5001 OBU Standard | Onboard Unit Standard for Connected Vehicles | Vehicle |
System Requirements
| No System Requirements |