< < PS09.2 : PS09.3 : PS10.1 > >
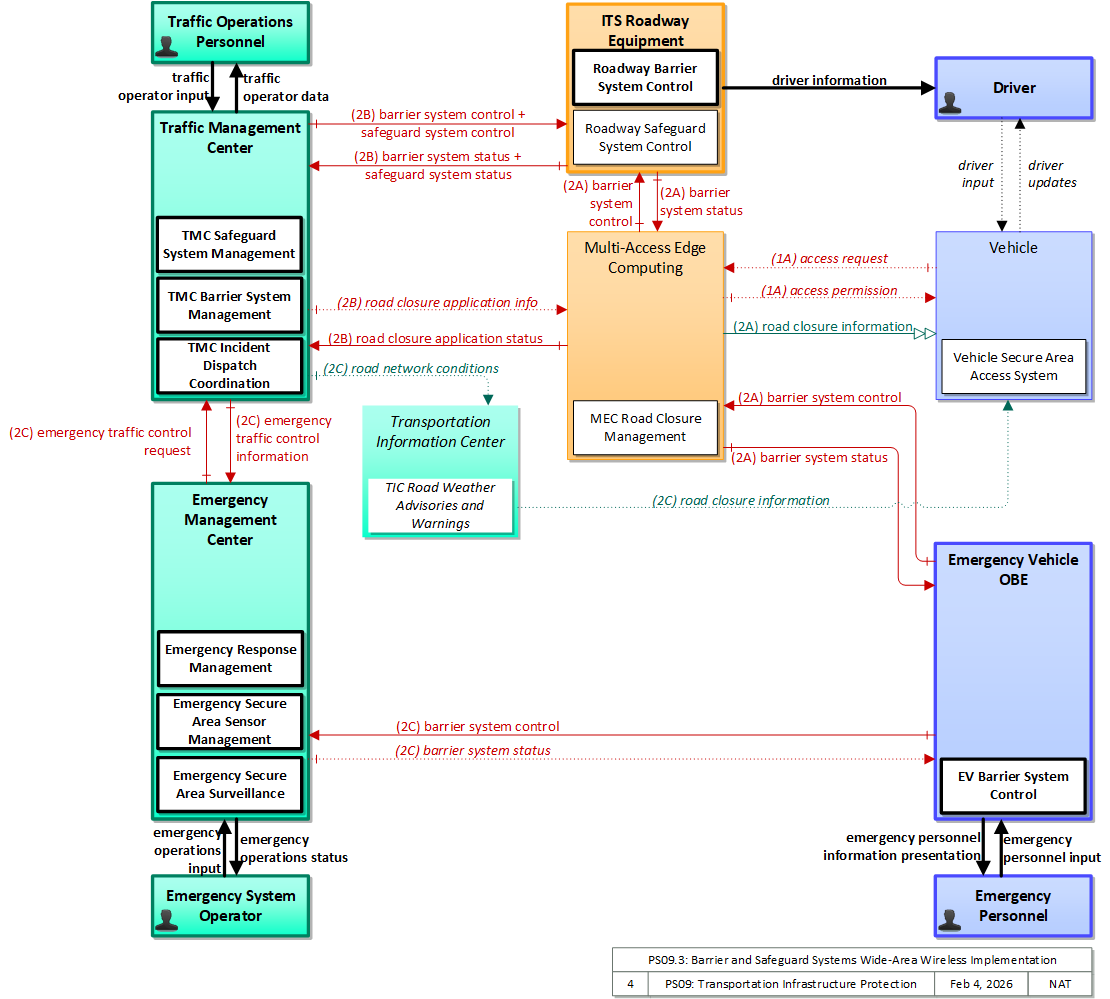
PS09.3: Barrier and Safeguard Systems Wide-Area Wireless Implementation
Includes barrier and safeguard systems to control access, preclude an incident, and mitigate the impact of an incident if it occurs. Wide-area wireless communications are used to communicate with barrier and safeguard systems, using a MEC to efficiently support local communications with field equipment, if needed.
Relevant Regions: Australia, Canada, European Union, and United States
- Enterprise
- Functional
- Physical
- Goals and Objectives
- Needs and Requirements
- Sources
- Security
- Standards
- System Requirements
Enterprise
Development Stage Roles and Relationships
Installation Stage Roles and Relationships
Operations and Maintenance Stage Roles and Relationships
(hide)
| Source | Destination | Role/Relationship |
|---|
Functional
This service package includes the following Functional View PSpecs:
Physical
The physical diagram can be viewed in SVG or PNG format and the current format is SVG.SVG Diagram
PNG Diagram
Includes Physical Objects:
| Physical Object | Class | Description |
|---|---|---|
| Driver | Vehicle | The 'Driver' represents the person that operates a vehicle on the roadway. Included are operators of private, transit, commercial, and emergency vehicles where the interactions are not particular to the type of vehicle (e.g., interactions supporting vehicle safety applications). The Driver originates driver requests and receives driver information that reflects the interactions which might be useful to all drivers, regardless of vehicle classification. Information and interactions which are unique to drivers of a specific vehicle type (e.g., fleet interactions with transit, commercial, or emergency vehicle drivers) are covered by separate objects. |
| Emergency Management Center | Center | The 'Emergency Management Center' represents systems that support incident management, disaster response and evacuation, security monitoring, and other security and public safety-oriented ITS applications. It includes the functions associated with fixed and mobile public safety communications centers including public safety call taker and dispatch centers operated by police (including transit police), fire, and emergency medical services. It includes the functions associated with Emergency Operations Centers that are activated at local, regional, state, and federal levels for emergencies and the portable and transportable systems that support Incident Command System operations at an incident. This Center also represents systems associated with towing and recovery, freeway service patrols, HAZMAT response teams, and mayday service providers. It manages sensor and surveillance equipment used to enhance transportation security of the roadway infrastructure (including bridges, tunnels, interchanges, and other key roadway segments) and the public transportation system (including transit vehicles, public areas such as transit stops and stations, facilities such as transit yards, and transit infrastructure such as rail, bridges, tunnels, or bus guideways). It provides security/surveillance services to improve traveler security in public areas not a part of the public transportation system. It monitors alerts, advisories, and other threat information and prepares for and responds to identified emergencies. It coordinates emergency response involving multiple agencies with peer centers. It stores, coordinates, and utilizes emergency response and evacuation plans to facilitate this coordinated response. Emergency situation information including damage assessments, response status, evacuation information, and resource information are shared The Emergency Management Center also provides a focal point for coordination of the emergency and evacuation information that is provided to the traveling public, including wide-area alerts when immediate public notification is warranted. It tracks and manages emergency vehicle fleets using real-time road network status and routing information from the other centers to aid in selecting the emergency vehicle(s) and routes, and works with other relevant centers to tailor traffic control to support emergency vehicle ingress and egress, implementation of special traffic restrictions and closures, evacuation traffic control plans, and other special strategies that adapt the transportation system to better meet the unique demands of an emergency. |
| Emergency Personnel | Vehicle | 'Emergency Personnel' represents personnel that are responsible for police, fire, emergency medical services, towing, service patrols, and other special response team (e.g., hazardous material clean-up) activities at an incident site. These personnel are associated with the Emergency Vehicle during dispatch to the incident site, but often work independently of the Emergency Vehicle while providing their incident response services. |
| Emergency System Operator | Center | 'Emergency System Operator' represents the public safety personnel that monitor emergency requests, (including those from the E911 Operator) and set up pre-defined responses to be executed by an emergency management system. The operator may also override predefined responses where it is observed that they are not achieving the desired result. This also includes dispatchers who manage an emergency fleet (police, fire, ambulance, HAZMAT, etc.) or higher order emergency managers who provide response coordination during emergencies. |
| Emergency Vehicle OBE | Vehicle | The 'Emergency Vehicle On-Board Equipment' (OBE) resides in an emergency vehicle and provides the processing, storage, and communications functions that support public safety-related connected vehicle applications. It represents a range of vehicles including those operated by police, fire, and emergency medical services. In addition, it represents other incident response vehicles including towing and recovery vehicles and freeway service patrols. It includes two-way communications to support coordinated response to emergencies. A separate 'Vehicle OBE' physical object supports the general vehicle safety and driver information capabilities that apply to all vehicles, including emergency vehicles. The Emergency Vehicle OBE supplements these general capabilities with capabilities that are specific to emergency vehicles. |
| ITS Roadway Equipment | Field | 'ITS Roadway Equipment' represents the ITS equipment that is distributed on and along the roadway that monitors and controls traffic and monitors and manages the roadway. This physical object includes traffic detectors, environmental sensors, traffic signals, highway advisory radios, dynamic message signs, CCTV cameras and video image processing systems, grade crossing warning systems, and ramp metering systems. Lane management systems and barrier systems that control access to transportation infrastructure such as roadways, bridges and tunnels are also included. This object also provides environmental monitoring including sensors that measure road conditions, surface weather, and vehicle emissions. Work zone systems including work zone surveillance, traffic control, driver warning, and work crew safety systems are also included. |
| Multi-Access Edge Computing | Field | 'Multi-Access Edge Computing' ((MEC) previously known as mobile edge computing) represents computing devices that operate and are managed like a cloud server, but are deployed at the edge of a network (typically a cellular network, but it could be any network). While not in strict proximity to the transportation network, these systems do benefit from vastly decreased distances to the roadway compared to central systems, and so can provide lower latency than strictly backoffice systems |
| Traffic Management Center | Center | The 'Traffic Management Center' monitors and controls traffic and the road network. It represents centers that manage a broad range of transportation facilities including freeway systems, rural and suburban highway systems, and urban and suburban traffic control systems. It communicates with ITS Roadway Equipment and Connected Vehicle Roadside Equipment (RSE) to monitor and manage traffic flow and monitor the condition of the roadway, surrounding environmental conditions, and field equipment status. It manages traffic and transportation resources to support allied agencies in responding to, and recovering from, incidents ranging from minor traffic incidents through major disasters. |
| Traffic Operations Personnel | Center | 'Traffic Operations Personnel' represents the people that operate a traffic management center. These personnel interact with traffic control systems, traffic surveillance systems, incident management systems, work zone management systems, and travel demand management systems. They provide operator data and command inputs to direct system operations to varying degrees depending on the type of system and the deployment scenario. |
| Transportation Information Center | Center | The 'Transportation Information Center' collects, processes, stores, and disseminates transportation information to system operators and the traveling public. The physical object can play several different roles in an integrated ITS. In one role, the TIC provides a data collection, fusing, and repackaging function, collecting information from transportation system operators and redistributing this information to other system operators in the region and other TICs. In this information redistribution role, the TIC provides a bridge between the various transportation systems that produce the information and the other TICs and their subscribers that use the information. The second role of a TIC is focused on delivery of traveler information to subscribers and the public at large. Information provided includes basic advisories, traffic and road conditions, transit schedule information, yellow pages information, ride matching information, and parking information. The TIC is commonly implemented as a website or a web-based application service, but it represents any traveler information distribution service. |
| Vehicle | Vehicle | This 'Vehicle' physical object is used to model core capabilities that are common to more than one type of Vehicle. It provides the vehicle-based general sensory, processing, storage, and communications functions that support efficient, safe, and convenient travel. Many of these capabilities (e.g., see the Vehicle Safety service packages) apply to all vehicle types including personal vehicles (including motorcycles), commercial vehicles, emergency vehicles, transit vehicles, and maintenance vehicles. From this perspective, the Vehicle includes the common interfaces and functions that apply to all motorized vehicles. The radio(s) supporting V2V and V2I communications are a key component of the Vehicle. Both one-way and two-way communications options support a spectrum of information services from basic broadcast to advanced personalized information services. Advanced sensors, processors, enhanced driver interfaces, and actuators complement the driver information services so that, in addition to making informed mode and route selections, the driver travels these routes in a safer and more consistent manner. This physical object supports all six levels of driving automation as defined in SAE J3016. Initial collision avoidance functions provide 'vigilant co-pilot' driver warning capabilities. More advanced functions assume limited control of the vehicle to maintain lane position and safe headways. In the most advanced implementations, this Physical Object supports full automation of all aspects of the driving task, aided by communications with other vehicles in the vicinity and in coordination with supporting infrastructure subsystems. |
Includes Functional Objects:
| Functional Object | Description | Physical Object |
|---|---|---|
| Emergency Response Management | 'Emergency Response Management' provides the strategic emergency response capabilities and broad inter-agency interfaces that are implemented for extraordinary incidents and disasters that require response from outside the local community. It provides the functional capabilities and interfaces commonly associated with Emergency Operations Centers. It develops and stores emergency response plans and manages overall coordinated response to emergencies. It monitors real-time information on the state of the regional transportation system including current traffic and road conditions, weather conditions, special event and incident information. It tracks the availability of resources and assists in the appropriate allocation of these resources for a particular emergency response. It also provides coordination between multiple allied agencies before and during emergencies to implement emergency response plans and track progress through the incident. It also coordinates with the public through the Emergency Telecommunication Systems (e.g., Reverse 911). It coordinates with public health systems to provide the most appropriate response for emergencies involving biological or other medical hazards. | Emergency Management Center |
| EV Barrier System Control | 'EV Barrier System Control' provides local control of automatic or remotely controlled gates and other barrier systems from an emergency vehicle. Using this capability, emergency personnel can open and close barriers without leaving the vehicle, using V2I Communications to control the barriers. | Emergency Vehicle OBE |
| MEC Road Closure Management | 'MEC Road Closure Management' communicates with qualified Connected Vehicles and barrier control systems to support local road closure management. It validates and requests implementation of road closure requests. During a closure, it can also support selective access to the closed area, only granting entry permission to allowed vehicles. | Multi-Access Edge Computing |
| Roadway Barrier System Control | 'Roadway Barrier System Control' includes the field equipment that controls barrier systems used to control access to transportation facilities and infrastructure. Barrier systems include automatic or remotely controlled gates, barriers and other access control systems. | ITS Roadway Equipment |
| Roadway Safeguard System Control | 'Roadway Safeguard System Control' includes field equipment that controls safeguard systems for transportation facilities and infrastructure. Safeguard systems include blast shields, exhaust systems and other automatic or remotely controlled systems intended to mitigate the impact of an incident. | ITS Roadway Equipment |
| TIC Road Weather Advisories and Warnings | 'TIC Road Weather Advisories and Warnings' collects, aggregates, and processes environmental situation data (aka environmental probe data) from connected vehicles. Environmental situation data may be collected through direct wide area wireless communications with vehicles or through short range communications equipment at the roadside. Aggregated environmental conditions information are distributed to other centers that use the information to support transportation operations and traveler information services. | Transportation Information Center |
| TMC Barrier System Management | 'TMC Barrier System Management' remotely monitors and controls barrier systems for transportation facilities and infrastructure under control of center personnel. Barrier systems include automatic or remotely controlled gates, barriers and other access control systems. It also provides an interface to other centers to allow monitoring and control of the barriers from other centers (e.g., public safety or emergency operations centers). | Traffic Management Center |
| TMC Incident Dispatch Coordination | 'TMC Incident Dispatch Coordination' formulates and manages an incident response that takes into account the incident potential, incident impacts, and resources required for incident management. It provides information to support dispatch and routing of emergency response and service vehicles as well as coordination with other cooperating agencies. It provides access to traffic management resources that provide surveillance of the incident, traffic control in the surrounding area, and support for the incident response. It monitors the incident response and collects performance measures such as incident response and clearance times. | Traffic Management Center |
| TMC Safeguard System Management | 'TMC Safeguard System Management' remotely monitors and controls safeguard systems for transportation facilities and infrastructure. Safeguard systems include blast shielding, exhaust systems and other automatic or remotely controlled systems intended to mitigate the impact of an incident. When access to a transportation facility is impacted by the activation of a safeguard system, impacted systems and travelers are notified. | Traffic Management Center |
| Vehicle Secure Area Access System | 'Vehicle Secure Area Access System' provides access to secure areas such as shipping yards, warehouses, airports, transit-only ramps, parking gates and other areas. It accepts inputs from the vehicle driver that include the necessary identity information and uses this information to generate the request to activate a barrier to gain access to the area. | Vehicle |
Includes Information Flows:
| Information Flow | Description |
|---|---|
| access permission | Information returned indicating whether permission for access is granted and instructions for proceeding. |
| access request | Request for access to an access-controlled transportation facility. |
| barrier system control | Information used to configure and control barrier systems that are represented by gates, barriers and other automated or remotely controlled systems used to manage entry to roadways. |
| barrier system status | Current operating status of barrier systems. Barrier systems represent gates, barriers and other automated or remotely controlled systems used to manage entry to roadways. Status of the systems includes operating condition and current operational state. |
| driver information | Regulatory, warning, guidance, and other information provided to the driver to support safe and efficient vehicle operation. |
| driver input | Driver input to the vehicle on-board equipment including configuration data, settings and preferences, interactive requests, and control commands. |
| driver updates | Information provided to the driver including visual displays, audible information and warnings, and haptic feedback. The updates inform the driver about current conditions, potential hazards, and the current status of vehicle on-board equipment. |
| emergency operations input | Emergency operator input supporting call taking, dispatch, emergency operations, security monitoring, and other operations and communications center operator functions. |
| emergency operations status | Presentation of information to the operator including emergency operations data, supporting a range of emergency operating positions including call taker, dispatch, emergency operations, security monitoring, and various other operations and communications center operator positions. |
| emergency personnel information presentation | Presentation of information to emergency personnel in the field including dispatch information, incident information, current road network conditions, device status, and other supporting information. |
| emergency personnel input | User input from emergency personnel in the field including dispatch coordination, incident status information, and remote device control requests. |
| emergency traffic control information | Status of a special traffic control strategy or system activation implemented in response to an emergency traffic control request, a request for emergency access routes, a request for evacuation, a request to activate closure systems, a request to employ driver information systems to support public safety objectives, or other special requests. Identifies the selected traffic control strategy and system control status. |
| emergency traffic control request | Special request to preempt the current traffic control strategy in effect at one or more signalized intersections or highway segments, activate traffic control and closure systems such as gates and barriers, activate safeguard systems, or use driver information systems. For example, this flow can request all signals to red-flash, request a progression of traffic control preemptions along an emergency vehicle route, request a specific evacuation traffic control plan, request activation of a road closure barrier system, or place a public safety or emergency-related message on a dynamic message sign. |
| road closure application info | Road closure signing application configuration data and messaging parameters. This flow identifies the vehicles that may initiate the road closure. This flow also provides access lists, groups, or classifications where selected vehicles are to be allowed access to the closed area. |
| road closure application status | Road closure application status reported by the RSE. This includes current operational state and status of the RSE, closure status, and a log of closure commands received and issued. For closures that allow entry by selected vehicles, this flow provides an access log identifying vehicles that have requested access with access status. |
| road closure information | Geo-fenced road closure information provided to vehicles. This flow provides information about the road closure with diversion information. |
| road network conditions | Current and forecasted traffic information, road and weather conditions, and other road network status. Either raw data, processed data, or some combination of both may be provided by this flow. Information on diversions and alternate routes, closures, and special traffic restrictions (lane/shoulder use, weight restrictions, width restrictions, HOV requirements) in effect is included. |
| safeguard system control | Data that controls safeguard systems (remotely controlled equipment used to mitigate the impact of incidents on transportation infrastructure, such as blast shields, exhaust systems, etc.). |
| safeguard system status | Current operating status of safeguard systems (remotely controlled equipment used to mitigate the impact of incidents on transportation infrastructure, such as blast shields, exhaust systems, etc.). Status of the systems includes operating condition and current operational state. |
| traffic operator data | Presentation of traffic operations data to the operator including traffic conditions, current operating status of field equipment, maintenance activity status, incident status, video images, security alerts, emergency response plan updates and other information. This data keeps the operator appraised of current road network status, provides feedback to the operator as traffic control actions are implemented, provides transportation security inputs, and supports review of historical data and preparation for future traffic operations activities. |
| traffic operator input | User input from traffic operations personnel including requests for information, configuration changes, commands to adjust current traffic control strategies (e.g., adjust signal timing plans, change DMS messages), and other traffic operations data entry. |
Goals and Objectives
Associated Planning Factors and Goals
| Planning Factor | Goal |
|---|
Associated Objective Categories 
| Objective Category |
|---|
Associated Objectives and Performance Measures 
| Objective | Performance Measure |
|---|

Needs and Requirements
| Need | Functional Object | Requirement | ||
|---|---|---|---|---|
Related Sources
| Document Name | Version | Publication Date |
|---|---|---|
| None |
Security
In order to participate in this service package, each physical object should meet or exceed the following security levels.
| Physical Object Security | ||||
|---|---|---|---|---|
| Physical Object | Confidentiality | Integrity | Availability | Security Class |
| Emergency Management Center | Moderate | High | Moderate | Class 3 |
| Emergency Vehicle OBE | Moderate | High | Moderate | Class 3 |
| ITS Roadway Equipment | High | High | High | Class 5 |
| Multi-Access Edge Computing | Moderate | High | Moderate | Class 3 |
| Traffic Management Center | High | High | High | Class 5 |
| Transportation Information Center | Low | Moderate | Moderate | Class 1 |
| Vehicle | Moderate | Moderate | Moderate | Class 2 |
In order to participate in this service package, each information flow triple should meet or exceed the following security levels.
| Information Flow Security | |||||
|---|---|---|---|---|---|
| Source | Destination | Information Flow | Confidentiality | Integrity | Availability |
| Basis | Basis | Basis | |||
| Driver | Vehicle | driver input | Moderate | High | High |
| Data included in this flow may include origin and destination information, which should be protected from other's viewing as it may compromise the driver's privacy. | Commands from from the driver to the vehicle must be correct or the vehicle may behave in an unpredictable and possibly unsafe manner | Commands must always be able to be given or the driver has no control. | |||
| Emergency Management Center | Emergency System Operator | emergency operations status | Moderate | High | High |
| Emergency system controls should not be casually viewable as they impact the availability of emergency services, which if known could be leveraged for illegal activity. | Backoffice operations flows should generally be correct and available as these are the primary interface between operators and system. | Backoffice operations flows should generally be correct and available as these are the primary interface between operators and system. | |||
| Emergency Management Center | Emergency Vehicle OBE | barrier system status | Moderate | High | Moderate |
| Related to the control flow, however the data is directly observable and generally widely known. Difficult to justify obfuscation. | Status of barrier systems has direct human-safety related impact, that if performed incorrectly could lead to catastrophic incidents. | These systems need to operated when demanded or mobility will be restricted. However, manual processes should always be in place to compensate for a loss in connectivity, and to provide a secondary check for safety purposes anyway. | |||
| Emergency Management Center | Traffic Management Center | emergency traffic control request | Moderate | High | Moderate |
| These requests could be used to track the specific route that an emergency vehicle is planning on taking. | False requests here could bring the traffic system to a standstill by making all of the lights red. Additionally, the system must be able to trust these requests, and know that they came from an authorized source. | These messages are important for the system to operate properly. Additionally, the system must know if messages are not received so that it can act accordingly. | |||
| Emergency Personnel | Emergency Vehicle OBE | emergency personnel input | Moderate | Moderate | Moderate |
| Some of the information, such as incident status information, is sensitive, and should be protected. | The system must know that these requests came from actual Emergency Personal. Additionally, incorrect information here may lead to the system responding incorrectly to the incident | These messages are important for the system to operate properly. Additionally, the system must know if messages are not received so that it can act accordingly. | |||
| Emergency System Operator | Emergency Management Center | emergency operations input | Moderate | High | High |
| Emergency system controls should not be casually viewable as they impact the availability of emergency services, which if known could be leveraged for illegal activity. | Backoffice operations flows should generally be correct and available as these are the primary interface between operators and system. | Backoffice operations flows should generally be correct and available as these are the primary interface between operators and system. | |||
| Emergency Vehicle OBE | Emergency Management Center | barrier system control | Moderate | High | Moderate |
| Control flows need to be obfuscated, lest a hostile individual learn how to control these systems. Barrier systems in particular present a safety risk if compromised, and could have a significant safety and mobility impact. | Control of barrier systems has direct human-safety related impact, that if performed incorrectly could lead to catastrophic incidents. | These systems need to operated when demanded or mobility will be restricted. However, manual processes should always be in place to compensate for a loss in connectivity, and to provide a secondary check for safety purposes anyway. | |||
| Emergency Vehicle OBE | Emergency Personnel | emergency personnel information presentation | Moderate | Moderate | Moderate |
| Some of this information, such as incident information, is sensitive and should be protected. | This information could affect how the Emergency Personnel respond to the event, and should be as accurate as possible. | This information needs to be available for the Emergency Personnel in order for them to respond accurately to the system. If they do not acknowledge this information, dispatch needs to know, so they can attempt to contact the Emergency Personnel via another channel, such as radio. | |||
| Emergency Vehicle OBE | Multi-Access Edge Computing | barrier system control | Moderate | High | Moderate |
| Control flows need to be obfuscated, lest a hostile individual learn how to control these systems. Barrier systems in particular present a safety risk if compromised, and could have a significant safety and mobility impact. | Control of barrier systems has direct human-safety related impact, that if performed incorrectly could lead to catastrophic incidents. | These systems need to operated when demanded or mobility will be restricted. However, manual processes should always be in place to compensate for a loss in connectivity, and to provide a secondary check for safety purposes anyway. | |||
| ITS Roadway Equipment | Driver | driver information | Not Applicable | High | Moderate |
| This data is sent to all drivers and is also directly observable, by design. | This is the primary signal trusted by the driver to decide whether to go through the intersection and what speed to go through the intersection at; if it’s wrong, accidents could happen. | If the lights are out you have to get a policeman to direct traffic – expensive and inefficient and may cause a cascading effect due to lack of coordination with other intersections. | |||
| ITS Roadway Equipment | Multi-Access Edge Computing | barrier system status | Moderate | High | Moderate |
| Related to the control flow, however the data is directly observable and generally widely known. Difficult to justify obfuscation. | Status of barrier systems has direct human-safety related impact, that if performed incorrectly could lead to catastrophic incidents. | These systems need to operated when demanded or mobility will be restricted. However, manual processes should always be in place to compensate for a loss in connectivity, and to provide a secondary check for safety purposes anyway. If no manual system exists, then some instances will be HIGH. | |||
| ITS Roadway Equipment | Traffic Management Center | barrier system status | Moderate | High | Moderate |
| Related to the control flow, however the data is directly observable and generally widely known. Difficult to justify obfuscation. | Status of barrier systems has direct human-safety related impact, that if performed incorrectly could lead to catastrophic incidents. | These systems need to operated when demanded or mobility will be restricted. However, manual processes should always be in place to compensate for a loss in connectivity, and to provide a secondary check for safety purposes anyway. | |||
| ITS Roadway Equipment | Traffic Management Center | safeguard system status | Moderate | High | Moderate |
| Related to the control flow, however the data is directly observable and generally widely known. Difficult to justify obfuscation. | Status of barrier systems has direct human-safety related impact, that if performed incorrectly could lead to catastrophic incidents. | These systems need to operated when demanded or mobility will be restricted. However, manual processes should always be in place to compensate for a loss in connectivity, and to provide a secondary check for safety purposes anyway. If no manual system exists, then some instances will be HIGH (for example, exhaust systems in tunnels). | |||
| Multi-Access Edge Computing | Emergency Vehicle OBE | barrier system status | Moderate | High | Moderate |
| Related to the control flow, however the data is directly observable and generally widely known. Difficult to justify obfuscation. | Status of barrier systems has direct human-safety related impact, that if performed incorrectly could lead to catastrophic incidents. | These systems need to operated when demanded or mobility will be restricted. However, manual processes should always be in place to compensate for a loss in connectivity, and to provide a secondary check for safety purposes anyway. If no manual system exists, then some instances will be HIGH. | |||
| Multi-Access Edge Computing | ITS Roadway Equipment | barrier system control | Moderate | High | Moderate |
| Control flows need to be obfuscated, lest a hostile individual learn how to control these systems. Barrier systems in particular present a safety risk if compromised, and could have a significant safety and mobility impact. | Control of barrier systems has direct human-safety related impact, that if performed incorrectly could lead to catastrophic incidents. | These systems need to operated when demanded or mobility will be restricted. However, manual processes should always be in place to compensate for a loss in connectivity, and to provide a secondary check for safety purposes anyway. | |||
| Multi-Access Edge Computing | Traffic Management Center | road closure application status | Moderate | Moderate | Low |
| This information could be of interest to a malicious individual who is attempting to determine the best way to accomplish a crime. As such it would be best to not make it easily accessible. | A delay in reporting this may cause a delay in necessary maintenance, but (a) this is not time-critical and (b) there are other channels for reporting malfunctioning. Additionally, there is a message received notification, which means that RSE can ensure that all intersection safety issues are delivered. | A delay in reporting this may cause a delay in necessary maintenance, but (a) this is not time-critical and (b) there are other channels for reporting malfunctioning. Additionally, there is a message received notification, which means that RSE can ensure that all intersection safety issues are delivered. | |||
| Multi-Access Edge Computing | Vehicle | access permission | Moderate | Moderate | Moderate |
| This indicates whether the OBE-equipped vehicle may proceed with a requested action. Such information is intended only for the OBE, and if observed by a third party may reveal the OBE operator's intent, so should be protected. | Incorrect permission may deny rightful access or appear to grant access when it should not. If rightful access is mission critical this should be HIGH. An incorrect granting of access will likely be subsequently denied by other means (guards, gates, etc.), which justifies leaving this at MODERATE. | Importance rationale tied to Integrity requirement. If critical, there should be other mechanisms. | |||
| Multi-Access Edge Computing | Vehicle | road closure information | Low | Moderate | Moderate |
| Lane closure information is intended for broadcast and public consumption. | Data should be consistent with observed reality, so it should be protected appropriately, otherwisee users may lose confidence in and ignore this flow in the future. | While useful, this information is available through a variety of means. | |||
| Traffic Management Center | Emergency Management Center | emergency traffic control information | Moderate | High | Moderate |
| This can potentially include sensitive information, such as response information to emergencies. | Invalid messages could lead to an unauthorized user gaining transit signal priority at an intersection. This could also be used to bring traffic to a standstill, which could lead to a large financial impact on the community. | These messages are important to help with the transit signal priority application. Without them, it will not work. However, if these signals are not received, the Emergency Vehicle can still navigate through the intersection using Lights and Sirens. The TMC should have an acknowledgement of the receipt of a message. | |||
| Traffic Management Center | ITS Roadway Equipment | barrier system control | Moderate | High | Moderate |
| Control flows need to be obfuscated, lest a hostile individual learn how to control these systems. Barrier systems in particular present a safety risk if compromised, and could have a significant safety and mobility impact. | Control of barrier systems has direct human-safety related impact, that if performed incorrectly could lead to catastrophic incidents. | These systems need to operated when demanded or mobility will be restricted. However, manual processes should always be in place to compensate for a loss in connectivity, and to provide a secondary check for safety purposes anyway. | |||
| Traffic Management Center | ITS Roadway Equipment | safeguard system control | High | High | High |
| Control flows, even for seemingly innocent devices, should be kept confidential to minimize attack vectors. While an individual installation may not be particularly impacted by a cyberattack of its sensor network, another installation might be severely impacted, and different installations are likely to use similar methods, so compromising one leads to compromising all. | Control flows, even for seemingly innocent devices, should have MODERATE integrity at minimum, just to guarantee that intended control messages are received. Incorrect, corrupted, intercepted and modified control messages can or will result in target field devices not behaving according to operator intent. The severity of this depends on the type of device, which is why some devices are set MODERATE and some HIGH. | Control flow availability is related to the criticality of being able to remotely control the device. For most devices, this is MODERATE. For purely passive devices with no incident relationship, this will be LOW. All devices should have default modes that enable them to operate without backhaul connectivity, so no device warrants a HIGH. | |||
| Traffic Management Center | Multi-Access Edge Computing | road closure application info | Moderate | Moderate | Low |
| This is a control flow, so should be obfuscated to make it more difficult for a 3rd party to manipulate the RSE. | Control parameters need to be correct and not corrupted so that the owner of the RSE and the receiver of the RSE's data get what they need from it. | This information probably does not need to be changed very often, and if it is not available then likely the flow it controls (emissions data flows to the DDS/EMC) are down as well. | |||
| Traffic Management Center | Traffic Operations Personnel | traffic operator data | Moderate | Moderate | Moderate |
| Backoffice operations flows should have minimal protection from casual viewing, as otherwise imposters could gain illicit control or information that should not be generally available. | Information presented to backoffice system operators must be consistent or the operator may perform actions that are not appropriate to the real situation. | The backoffice system operator should have access to system operation. If this interface is down then control is effectively lost, as without feedback from the system the operator has no way of knowing what is the correct action to take. | |||
| Traffic Management Center | Transportation Information Center | road network conditions | Low | Moderate | Moderate |
| No harm should come from seeing this data, as it is eventually intended for public consumption. | While accuracy of this data is important for decision making purposes, applications should be able to corroborate the data in many instances. Thus MODERATE generally. | Depends on the application; if mobility decisions that affect large numbers of travelers are made based on this data, then it is MODERATE. In more modest circumstances, it may be LOW. | |||
| Traffic Operations Personnel | Traffic Management Center | traffic operator input | Moderate | High | High |
| Backoffice operations flows should have minimal protection from casual viewing, as otherwise imposters could gain illicit control or information that should not be generally available. | Backoffice operations flows should generally be correct and available as these are the primary interface between operators and system. | Backoffice operations flows should generally be correct and available as these are the primary interface between operators and system. | |||
| Transportation Information Center | Vehicle | road closure information | Low | Moderate | Moderate |
| Lane closure information is intended for broadcast and public consumption. | Data should be consistent with observed reality, so it should be protected appropriately, otherwisee users may lose confidence in and ignore this flow in the future. | While useful, this information is available through a variety of means. | |||
| Vehicle | Driver | driver updates | Not Applicable | Moderate | Moderate |
| This data is informing the driver about the safety of a nearby area. It should not contain anything sensitive, and does not matter if another person can observe it. | This is the information that is presented to the driver. If they receive incorrect information, they may act in an unsafe manner. However, there are other indicators that would alert them to any hazards, such as an oncoming vehicle or crossing safety lights. | If this information is not made available to the driver, then the system has not operated correctly. | |||
| Vehicle | Multi-Access Edge Computing | access request | Moderate | Moderate | Moderate |
| This indicates the OBE-equipped vehicle's intent to perform a given action. Such information is intended only for the entity capable of granting access, and if observed by a third party may reveal the OBE operator's intent, so should be protected. | Incorrect permission may deny rightful access or appear to grant access when it should not. If rightful access is mission critical this should be HIGH. An incorrect granting of access will likely be subsequently denied by other means (guards, gates, etc.), which justifies leaving this at MODERATE. | Importance rationale tied to Integrity requirement. If critical, there should be other mechanisms. | |||
Standards
The following table lists the standards associated with physical objects in this service package. For standards related to interfaces, see the specific information flow triple pages. These pages can be accessed directly from the SVG diagram(s) located on the Physical tab, by clicking on each information flow line on the diagram.
| Name | Title | Physical Object |
|---|---|---|
| ISO 24100 Probe Vehicle Data Protection | Intelligent transport systems -- Basic principles for personal data protection in probe vehicle information services | Traffic Management Center |
| Transportation Information Center | ||
| ITE 5301 ATC ITS Cabinet | Intelligent Transportation System Standard Specification for Roadside Cabinets | ITS Roadway Equipment |
| NEMA TS 8 Cyber and Physical Security | Cyber and Physical Security for Intelligent Transportation Systems | ITS Roadway Equipment |
| Traffic Management Center | ||
| SAE J3361 Antenna requirements | V2X Antenna Coverage and Test Requirements for US FHWA Class 1 and Class 3-13 Class Vehicles | Emergency Vehicle OBE |
| Vehicle | ||
| SAE J5001 OBU Standard | Onboard Unit Standard for Connected Vehicles | Emergency Vehicle OBE |
| Vehicle |
System Requirements
| No System Requirements |